Era nell’aria, come gia’ parlato in questo articolo, lasciare l’SSH con la password di default sui telefoni sbloccati puo causare qualche problema. Infatti ecco qua pronto il primo worm per iphone che sfrutta questa “dimenticanza”.

Roma – In bilico tra amore diffuso e odio collettivo, gli anni ’80 hanno segnato in qualche modo una generazione, a partire da certi romanticismi sonori di nuovi crooner pel di carota. Come il fenomeno di Internet Rick Astley e il suo orecchiabile singolo Never Gonna Give You Up, che ha illustrato al mondo del web i segreti dell’ormai noto (e famigerato) rickrolling. E gli anni ’80 hanno segnato in qualche modo un ventunenne hacker australiano che ha deciso di diffondere il fascinoso viso di Astley attraverso un worm scritto di suo pugno, destinato alla propagazione tra un particolare gruppo di utenti iPhone nella terra dei canguri.
[ad]
La storia è iniziata alcuni giorni fa, quando un utente di un forum australiano ha riportato uno strano accadimento al suo Melafonino 3GS. Al risveglio, l’abituale foto del partner impostata come wallpaper era all’improvviso sparita, sostituita da una foto ammiccante di Rick Astley. Ikee non ti abbandonerà mai, recitava una scritta rossa in alto sullo sfondo del dispositivo. Analizzato da Sophos, azienda nel settore della sicurezza informatica, il codice sorgente del worm ha spiegato che il suo nome in codice è ikee virus, creato da ike_x ovvero un programmatore inoccupato di nome Ashley Town, da Wollogong, Australia.
L’utente iPhone non è rimasto particolarmente soddisfatto dello scambio di wallpaper, dal momento che gli è risultato impossibile tornare a quello precedente. Qualcuno gli ha fatto notare di essere stato iRickRoll’d, ma la burla ha lasciato presto il posto alla riflessione di Sophos sul worm e sulle sue conseguenze. Ike_x ha sfruttato una particolare vulnerabilità degli smartphone di Apple, venutasi a creare in seguito al loro sblocco per l’installazione di applicazioni non autorizzate. Il worm si è cioè propagato tra tutti quei dispositivi che hanno installato il software necessario a far girare una shell SSH,senza aver cambiato la root password di default: alpine.
Di conseguenza, il worm non ha toccato quegli utenti che non hanno modificato i propri smartphone o comunque cambiato la password di default una volta installato il software. È proprio sulla questione password che sembra essersi meravigliato l’hacker/cracker, interrogandosi sull’apparente stupidità di persone non troppo consapevoli degli innumerevoli rischi derivanti da password intercettabilissime. Come accaduto recentemente agli iPhone olandesi, i cui dati erano stati presi in ostaggio da un cracker che aveva chiesto agli utenti un riscatto di 5 euro per ottenere in cambio le istruzioni necessarie alla messa in sicurezza del telefono.
A proposito di istruzioni, Sophos ha pubblicato un messaggio da parte dell’hacker che era stato implementato all’interno del codice. “Nessuno legge più il dannato manuale?” si è chiesto Town, utilizzando il più eloquente acronimo RTFM. Si è scoperto che il ragazzo era annoiato, sicuramente e profondamente scosso da una verità da se stesso accertata: che 26 host su 27 da lui testati dotati di daemon SSH utilizzavano la password di default. Una mancanza d’accortezza certo pericolosa per gli utenti, soprattutto perché sembra che non tutti apprezzino svegliarsi la mattina guardando il viso di Rick Astley al posto di quello della dolce metà.
Mauro Vecchio – http://punto-informatico.it/2746872/PI/News/iphone-un-worm-che-non-ti-abbandona.aspx
Per proteggersi dal worm basta seguire questa semplice guida: http://www.f-secure.com/weblog/archives/cydia.htm
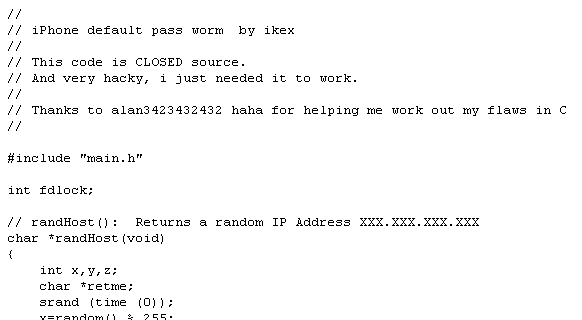
Alcuni spezzoni di codice del worm:

Qua di seguito abbiamo un intervista fatta all’autore del worm (ikee):
[09:02] <JD> Hi ikee 🙂 Thanks for joining me
[09:02] <ikee> nps
[09:03] <JD> Now, as you’re well aware, you wrote a virus that is infecting many iPhones in Australia. I guess the real question to start with is why?
[09:04] <ikee> First i was curious to how far something like this would actually spread, i think what most people were unaware of is the fact it IS a worm and every phone that got infected with it was spreading it (I initially only infected 3 phones when I woke up i checked google and found out a fair few people were hit with it)
[09:05] <ikee> Secondly i was quite amazed by the number of people who didn’t RTFM and change their default passwords.
[09:07] <JD> How far did you expect it to spread, exactly?
[09:08] <ikee> Well i didn’t think that many people would have not changed their passwords I was expecting to see maybe 10~ or so people, at first I was not even going to add the replicate/worm code but it was a learning experience and i got a tad carried away 🙂
[09:11] <JD> Are you aware that it has even started to replicate itself overseas?
[09:13] <ikee> I heard a few stories about it, that would have been sheer luck, the code itself is set to firstly scan the 3G IP range the phone is on, then Optus/Vodafone/Telstra’s IP Ranges (I think the reason Optus got hit so hard is because the other 2 are NAT’d) then a random 20 IP ranges. I’m guessing a few phones hit a range that another vulnerable phone was on.
[09:14] <ikee> (From another country)
[09:15] <JD> Well that was my next question: Why does it only seem to be hitting Optus here and Overseas (I was presuming from screenshots I’ve seen)… So you’re saying the Optus network is more vulnerable due to it not using NAT?
[09:17] <ikee> I don’t think it was an Optus fault (Being an Optus user I quite like the fact i can access my iPhone services from the outside world), I think it was mainly the fault of people being to lazy to change their passwords (It only takes a couple of seconds guys) and I hope this taught a few people that.
[09:18] <JD> So do you know exactly how many people are currently infected with the “ikee virus”?
[09:20] <ikee> I can only confirm how many my phone infected alone, which was 100+ phones. I think most of them fixed it (AND I’M HOPING THEY CHANGED THEIR PASSWORDS.)
[09:21] <JD> So your major defense seems to be that people left themselves vulnerable, Do you steal stuff from people’s houses if they leave the backdoor open?
[09:24] <ikee> I’ll answer your question with two questions, Have you ever used unprotected Wifi? and Technically I did not steal anything, have you ever littered on someone else’s property? (Smokers will definitely associate ;))
[09:25] <JD> Ok, I suppose I can personally admit to both of them, but it seems alot more to me like vandalism than littering, which isn’t something I would do
[09:27] <ikee> Personally I would class littering as vandalism (They definitely don’t want your rubbish there). I admit I probably pissed of a few people, but it was all in good fun (well ok for me anyway)
[09:30] <JD> So that explains why you decided to use Rick Astley. In my research, I’ve been reading about a similar virus (it seems) that contains a picture of an ‘asian child’ – I havn’t seen screenshots of this, but that’s how it is described. Are you also responsible for the “Asian Child virus”?
[09:32] <ikee> Ahh that was a quirk of my bad coding, the ‘virus’ itself has 4 variations and the first variation would resend its LockBackground.jpg to the victim. I did not comprehend that the infector might have not rebooted their phone after changing the LockBackground to something else (Causing them to send their changed lockbackground instead of Mr Astley)
[09:36] <JD> So it’s the same virus, but now containing a picture of someone’s loved one?
[09:37] <ikee> Yeah, that was definitely not the intended effect.
[09:39] <JD> Are you aware of the possible legal consequences of this (the ikee virus)? Are you concerned?
[09:40] <ikee> I’d like to think I’m aware, and also I highly doubt I’m in any real trouble (So no not concerned)
[09:43] <JD> James01 on Whirlpool asks: at least one person has reported being affected without a jailbreak – seems unlikely given the nature of the phone and what I have garned about the “virus” – is this possible, or are the reports unreliable/mistaken?
[09:44] <ikee> It only affects jailbroken phones, so people probably just got a little confused
[09:45] <JD> vanquish777 on Whirlpool says: What I want to know is, how did I get infected when I had SSH toggled off
[09:46] <ikee> You didn’t :), My guess is you had it on and when the ‘virus’ hit, it disabled sshd so when you checked it afterwards it appeared to be off
[09:47] <JD> Which reminds me, many people have said they are no longer able to disable SSH, is this intended to make sure you can do more damage to users?
[09:50] <ikee> This was a hard bit for me to do, until i hit this the virus was not destructive at all. My first intention was to change the root/mobile password to random strings, then embed the strings into the LockBackground. Unfortunately passwd uses a tty (and not stdin) for its new password:request (similar to ssh logins, which is why you might find sshpass in /bin/, i had to port it) so to stop the phone getting infected over and over again (and
[09:50] <ikee> someone else catching on and having mischief with peoples phones) I removed SSHD (cydia reinstall will rememdy the problem)
[09:51] <ikee> (Cydia reinstall of SSH not reinstall Cydia itself)
[09:53] <JD> So you’re saying that the only harm this virus causes is the removal of the SSH Daemon, which effectively, disables the initial problem?
[09:53] <ikee> Well that and the pretty background yes 🙂
[09:54] <JD> You mentioned that there are four versions/variants, what are the differences between them?
[09:55] <ikee> Variants A-C were quite similar and the ones most people have bought up. Variant D is fair bit different, it stores its files in a completely different place and hides itself a lot more (No random plists in LaunchDaemons)
[09:56] <JD> So you’re saying that the newest variant is more hidden, is it more malicious?
[09:57] <ikee> It is a lot more hidden, a think most phones tend to be more secured now so it should die pretty fast. It is a little more malicious it tampers with some Cydia files.
[10:01] <JD> Do Android users risk being infected? I’m guessing that the virus would only log in as root:alpine (the default root username and password for the iPhone OS IIRC)
[10:02] <ikee> AFAIK no unless a user decided to use the same passwords, Although there is a weird quirk I read about dropbear in Android allowing any password (A bug with libcrypt I believe) but I could be very wrong.
[10:03] <ikee> But even if an android phone was attacked the platform differences would not allow the code to be run 🙂
[10:04] <JD> Just out of curiousity, what do you call what i’ve named the “ikee virus”?
[10:05] <ikee> Its in a folder called POC-iWorm (Proof Of Concept) but I never named it (ikee virus works!)
[10:09] <JD> You yesterday agreed to send me the source code (and removal instructions), what variant will it contain?
[10:10] <ikee> C/D whatever version you want 🙂
[10:11] <JD> How about all four? I’ll obviously be placing them online – probably Google Code or similar
[10:13] <ikee> A-C was updated so I don’t have the first 2, I forked D from C. (I don’t know if its so wise posting the code online, nefarious people that otherwise would not have had the chance could modify it to be quite destructive)
[10:14] <JD> Perhaps, But it has become quite clear that there’s a load of people that are unsecure, and if anyone wants to do anything bad enough, they are already going to know how.
[10:15] <JD> I guess i’m hoping that the jailbreak software will soon have a “enter new root password” prompt for those users that are un-aware.
[10:15] <ikee> I’ll leave the choice up to you 🙂
[10:15] <ikee> I’d love to see that
[10:16] <ikee> or even a random password generated and displayed for the user to write down
[10:17] <JD> Yes, it would be very good. I had an iPod Touch a while ago, which I “jailbroke” – admittedly I didn’t change the default password. I guess i’m just glad it’s not me.
[10:17] <JD> Do you plan on making any further variants? If so, why?
[10:18] <ikee> No, I think the point has been made
[10:18] <JD> Have you developed anything PRODUCTIVE in the iPhone world?
[10:21] <ikee> I’m not too sure what others would class productive. I do not own a MAC or run OSX (Using a linux cross compile toolchain) so it makes it abit of a challenge to develop any applications utilising the UI (I have tho -.-). I think the best program ive developed for it for me was a remote debugging library that sends debug information over the network (Using MCAST)
[10:23] <JD> Do you have anything further to add (I’m having a mental blank on questions to ask right now)
[10:26] <ikee> I hope I did not piss off many people, this was a very simple problem and has an even simplier solution. I thought it was quite funny and I hope others did too 🙂
[10:27] <JD> You mentioned infecting only three iPhones to being with, when did that happen?
[10:28] <ikee> Around 4am November 6th (Yeah I have no life)
[10:31] <JD> To confirm, other than replicating itself, adding the picture of Rick Astley, and removing the SSH Daemon, are we likely to find anything else it does?
[10:32] <ikee> Nothing, and if you’re releasing the source code people will be able to see that 🙂
[10:33] <JD> Can you please explain to me, how an infected user would remove the different versions correctly?
[10:33] <JD> by correctly, I mean completely.
[10:33] <ikee> Sure, variants A-C store files in these directories
[10:34] <ikee> /bin/poc-bbot
[10:34] <ikee> /bin/sshpass
[10:34] <ikee> /var/log/youcanbeclosertogod.jpg
[10:34] <ikee> /var/mobile/LockBackground.jpg
[10:35] <ikee> /System/Library/LaunchDaemons/com.ikey.bbot.plist
[10:35] <ikee> /var/lock/bbot.lock
[10:35] <ikee> using an rm (in SSH or mobile-terminal on those files will remove it)
[10:36] <ikee> then reboot the phone, change your password and reinstall SSH
[10:36] <ikee> For variant D its abit different
[10:36] <ikee> The locations are
[10:37] <ikee> /usr/libexec/cydia/startup
[10:37] <ikee> /usr/libexec/cydia/startup.so
[10:37] <ikee> /usr/libexec/cydia/startup-helper
[10:37] <ikee> /System/Library/LaunchDaemons/com.saurik.Cydia.Startup.plist
[10:38] <ikee> Of course cydia used these files previously so you may need to reinstall it after deleting this files
[10:38] <ikee> *these
[10:38] <JD> So the D variant overwrites system files?
[10:39] <ikee> Overwrits cydia’s files
[10:39] <ikee> *Overwrites
[10:39] <JD> Sorry, I’m not an expert at the iPhone OS 😛
[10:39] <ikee> Neither 😛
[10:40] <JD> So none of your versions do contain any password changing commands?
[10:40] <JD> I mean, so when I provide uninstall instructions, I can tell them to use alpine as the password ?
[10:41] <ikee> None of the code changes passwords
[10:42] <JD> Thanks for your time ikee, and I really hope you do get into developing things that are productive sometime soon.
[10:42] <ikee> me too 🙂 and no problems
[10:42] <JD> Perhaps on the Android platform (Yes, I know, I’m a fanboy)
[10:42] <ikee> I just downloaded the x86 iso, so maybe 😛
[10:43] <JD> I’ll ask you more about that after I end this logging session, Cheers 🙂
[10:43] <ikee> Ciaoo
End of #Interview_Room buffer Sun Nov 08 10:43:58 2009
EDIT = Una novità doverosa sull’argomento.
E’ giunta voce che l’autore del work è stato recentemente assunto da una software house che sviluppa programmi per il melafonino…

2 replies on “Il primo worm per iPhone”
I have written a comprehensive solution to removing the iKee virus. I have tried it out on my iPhone. So it should work fine for you.
goto-> junqin1.blogspot.com/2009/11/ikee-iphone-worm.html
Thanks junQuin.
It may be helpfuel.